
 |
Neon-komputadórComputer Users Manual, Ministry of Foreign Affairs and Cooperation, Democratic Republic of East Timor
|
|
Languages EnglishPortuguese Index IntrodcutionChapter II: Networks and Communications Basic ConceptsModems Integrated Services Digital Network(ISDN) Leased-Lines CATV ("Cable Modems") Direct Subscriber Lines Network Interface Cards Network Typologies Repeaters, Hubs and Switches Bridges, Routers and Brouters Wireless Ethernet Modem Protocols OSI and TCP/IP Other Network Protocols TCP/IP Lower and Middle Layers TCP/IP Upper Layer: Applications The Internet Chapter III: Operating Systems Chapter IV: Applications Chapter V: Basic Coding and Programming Chapter VI: Basic System Administration Appendicies: Ministry Policy |
Ministry Hompage
Basic ConceptsComputer-mediated communications has fundamentally transformed the way that people interact over the decade, particularly once the Internet, previously reserved for higher education, specialist government and military agencies in advanced nations, became a ubiquitous and common part of everyday life. The World-Wide Web in particular, through easy to use web browsers, have allowed hundred of millions access to computer mediated communication. In addition to this global reach, almost every large scale organization in the world manages their computer systems through local area networks (LAN) and wide area networks (WAN). This chapter will explore both the hardware and software used in local area networks and the Internet. A network can be defined as two or more computer systems that share data or hardware resources. It can be as small as two computers that share the same printer, or as large as the Internet, which is through a single software protocol called transmission control protocol/internet protocol (TCP/IP), connects hundreds of millions of computers. One can be more specific and note that it must be the computers that share the data or resources - it's debatable whether two computers which share a printer via a switchbox really counts as a network because it's not the computers as such that determine the sharing. At the barest minimum, in order for a network to exist the following are required: (1) cables or wireless connections between two or more computers., (2) a set of communications rules known as a network protocol., (3) a network operating system to determines the sharing of resources between computers. The two main choices for a network protocol are Ethernet and Token Ring. Both are defined under the Institute of Electric and Electronic Engineers (IEEE) and are known as IEEE 802.3 and IEEE 802.5 respectively. Ethernet is most widely used protocol, with the Token-Ring protocol now mainly found on IBM mainframe systems. Token-Ring networks have relatively expensive Network Interface Cards (Nicks) and a bandwidth of 4mbps or 16 depending on the cable type. In contrast Ethernet is found on a range of computer systems and supports a variety of cable types in the original protocol, in particular coaxial, fiber optic and Unshielded Twisted Pair (UTP), although only UTP is supported in the most recent versions of the protocol. The earliest Ethernet had a bandwidth of 10mbps, the most common FastEthernet 100mbs and the latest version, Gigabyte Ethernet 1000mbps. Several conceptual types of network exist. A small network formed among computer systems in a single building is referred to a Local Area Network. When several LANs are connected together by fibre-optic, wireless or 'phone lines this is referred to as a Wide Area Network (WAN), or for a particularly large scale a Metropolitan Area Network (MAN). Any network that is connected to other networks through TCP/IP is part of the Internet. Further, there are Intranets, that is internal networks that use TCP/IP and Internet software such as web browsers and Extranets which share data to subscribed users only. Essentially there are two basic types of LANs - client/server networks and peer-to-peer networks. In a client/server network, each computer system is either a client or a server. The server shares resources among the client computers and runs a operating system with specialist applications for the sharing of resources. A client only communicates with servers, not other clients. In contrast in a peer-to-peer network every computer is equal and can communicate with every other computer. Peer-to-peer networks tend to be limited to less than 10 computers (in fact the Windows2000 Professional operating system imposes this as a limit). Any more than this and performance loss because noticeable. Also, on a peer-to-peer network security is a major issue because accessing one computer gives you the ability to access any other computer. Further client/server networks invariably have centralized backup and redundancy through multiple power supplies, disk arrays and so forth. For security and resource efficiency, in the Ministry of Foreign Affairs and Cooperation we use a client/server network. Our server is a Compaq ProLiant DL380 Generation 2 Server. Some of its key features include; dual processor capacity, up to 6 gigabytes of memory, with 2 gigabytes in support, Ultra3 RAID capability, backup tape capability, two embedded Fast Ethernet Network Information Cards and up to 5 SCSI hard drives (currently has three installed). Quite honestly, it isn't really that flash, but it serves our purpose. Connected to this server as clients are a number of computers that use the Windows 2000 operating system. For those computers that use Windows 98 however, the computers are logically arranged in workgroups. Fortunately Windows NT/2000 and Windows 98 use the same workgroup model for browsing resources, 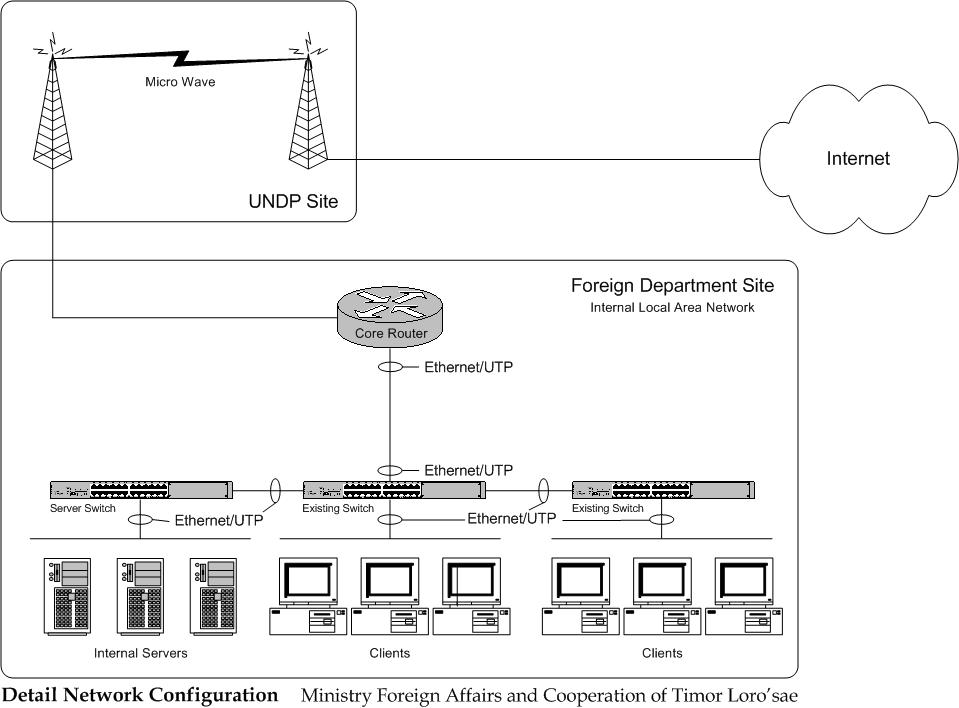 |
Ministry of Foreign Affairs and Cooperation, GPA Building #1, Ground Floor, Dili, East Timor
Website code and design by Lev Lafayette. Last update August 20, 2003